In IT compliance, control over data sharing is a major preventive step against accidental or intentional data breaches.
Here are a couple of cases that could have been avoided with better control over data sharing.
Roger Duronio was a UBS Wealth Management systems administrator. In 2006, he used a “logic bomb” to damage the company’s computer network. He was worried about the security of his job. He was expecting to receive a $50,000 bonus but received only $32,000. So, he used the logic bomb on the company’s stock. Because of this, 2,000 servers in UBS offices around the United States were down, and many couldn’t make trades for several weeks. The company suffered a loss of $3.1 million. Duronio was sentenced to 97 months in prison for the crime.
In 2012, there was a theft of 3.8 million unencrypted bank accounts in the South Carolina Department of Revenue by a Russian gang. They also stole the 4 million tax returns. This was due to a mistake by one employee who clicked on a link in an e-mail that enabled the channel to steal the employee’s credentials and access servers.
If there is so much risk in sharing the data, why is it required in the first place?
Data sharing is required for simply performing some jobs. Data is at the heart of all IT operations. Examples are operational staff who are responsible for processing transactions; people in support roles who have to troubleshoot data issues faced by customers.
Analysis, collaboration, research, concerns, problem resolution, and decision making all require data sharing. Data sharing reduces duplication of the same content. It also encourages analysing each other’s findings, perspectives, and results.
The pandemic has changed the whole perspective of the IT industry. Where only seniors or privileged employees were granted the right to work from home, due to the pandemic, everyone was working from home. This was a major change in the IT industry but was easily adopted throughout the world with the help of the latest and most secure technologies.
In fact, the growth rate was tremendously increased as compared to office work, as the work would be done in a flexible manner. But there were several risks as well, like accessing data from open networks without firewalls, without secure channels, etc. But now almost every threat has the latest technological solution, in software and hardware.
Threats can be monitored and controlled.
In my case, I am required to work on applications that handle sensitive data. It is for analysing the data, reporting on it, and sometimes for data correction.
To work on any of the above, I have to request access from my supervisor. He authorises it, then the System Administrator grants this access for a stipulated time. Access is granted on an alternate server which is a replica of the live server and not the actual live server. We call it a staging server. This server can only be accessed from a machine that is located in our office premise, which is behind a firewall. This helps to keep data safe and secure within the firewall.
Issues are analysed, replicated, fixed, and tested here before being deployed on the actual live server. This deployment process is done by our system admin securely.
Also, after completing the work, I immediately log out of the server, and the access is revoked by the System Admin.
Thus, in our organization, we have implemented several layers of security that prevent any data breach.
Let us look at the types of Data Sharing.
- Data Commons: One common dataset is shared by all and is accessible to the particular group whose work is dependent on this common dataset. These people could be researchers, scientists, etc., who can use this data for their findings or conclusions.
- Data Collaboratives: This could be private data that helps to make society and the environment better and is shared for social good.
- Data Marketplaces: These are online stores where data can be bought or sold.
- Data Trusts: O’Hara suggests that data trusts work within the law to provide ethical, architectural, and governance support for trustworthy data processing. Data trusts can be used for internal use only.
- Open data: This data is open to all. Furthermore, anybody can access and share it.
Some may ask, are data security and data sharing the opposite of each other.
A short answer to the question is, yes. Sharing is not always caring. But both have to go together hand in hand.
In general, the greatest data security risk is posed to organisations by insiders, as they have access to sensitive information on a regular basis and may know how that information is protected. If they want to steal it or leak the information, they can usually do so with far greater ease than outsiders. Furthermore, insiders may also accidentally leak data or otherwise put it at risk—something that outsiders typically cannot do.
What balance needs to be maintained while sharing data?
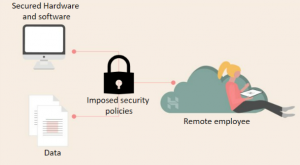
- Invest in reliable tools and software. You need to invest in reliable security tools and software to protect your data. This includes firewalls, antivirus software, anti-malware, and other monitoring tools for all types of devices.
- Establish cyber-security policies. Even with all these security tools in place, your first line of defence will always be your employees themselves. You should remind employees of their due diligence in protecting company data. This includes creating strong passwords for all devices and accounts, shutting down or signing out of devices after use, and keeping all software updated.
- Strengthen all passwords.
- Ensure all devices are protected.
- Securing a virtual workplace: Building an effective and efficient remote workplace can be tough, especially with all the cybersecurity threats going around. You really need to invest in the right tools and training for your remote employees. Otherwise, you risk exposing your business, workers, and customers to malicious attacks.
- Always provide limited/unimportant access to data for solving any data issues on local servers with changed and protected passwords.
- Encrypt data and communication.
- Always decide who sees what and to what period and extent.
With adequate care, it is possible to share the data to complete the work and not compromise any security aspects.
Resources:
https://hbr.org/2014/09/the-danger-from-within
https://id4d.worldbank.org/guide/data-protection-and-privacy-laws
https://datapitch.eu/toolkit-forms-of-data-sharing/#anchor11