As a provider of software solutions and in recent years hosting them on the cloud, we follow security standards diligently. In fact, that is a part of our deliverables to our customers. This write-up comes from the experience of being responsible for the security of our own information assets and those of our customers’.
Ensuring the protection of data is paramount for any company engaged in digital operations, where operational processes involve the creation and accumulation of digital media-stored information. Furthermore, there are mandatory standards set by various authorities, including industry regulatory bodies and global organizations, that must be adhered to. While they may occasionally appear burdensome, these standards are ultimately in the organization’s best interest, safeguarding data security and integrity.
By diligently and faithfully adhering to these standards, most risks concerning the protection of information assets are effectively mitigated. This practice is commonly referred to as Technology Compliance.
Regulatory bodies typically provide standards in the form of guidelines, suggestions, and best practices. A robust Governance, Risk, and Compliance (GRC) solution assists organizations in clear interpretation of these guidelines, eliminating any ambiguity during the translation into actionable tasks.
The A-P-I-A framework
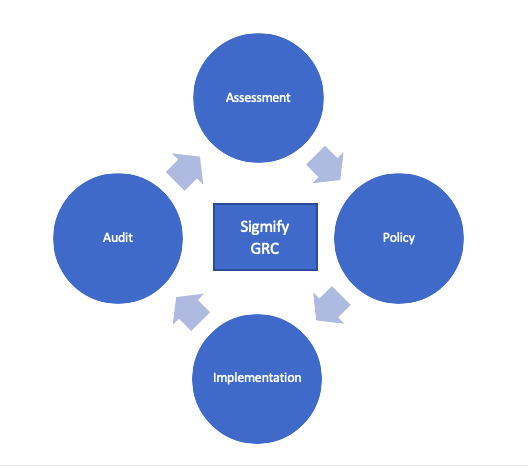
To adhere to these standards, Sigmify GRC employs a A-P-I-A framework. It provides a structured approach to ensure comprehensive mitigation of data security risks:
- Assessment (A): A gap assessment is a process in which a business compares its current performance to its performance expectations or goals.
- Policy (P): Policies are established to define the principles and objectives for data security.
- Implementation (I): Policies are translated into actionable controls, breaking them down into specific tasks and guidelines.
- Audit (A): The audit process verifies that the controls and policies are being followed as intended, providing assurance that data security measures are effective and compliant.
“Having policies without implementation is futile, leading to randomness. Implementation without policies is haphazard. Moreover, without regular reviews and audits, doubts may linger about whether implementation aligns with policies. These three elements collectively form the essential foundation of a GRC framework.”
Assessment:
The purpose of gap assessment is to help businesses identify any gaps or shortcomings that they might have in the organisation’s entire infrastructure including host, network, application and environmental controls. This assessment also includes a review of existing policies and procedures. A strategy can be created to overcome any issues and improve business operations. The steps in the Assessment include:
- Analyze the current state. Initially, a scope of assessment is defined. Then the current state of the scoped area is analyzed.
- Identify the ideal future state. The future state is defined with respect to the requirements of the applicable standard or framework.
- Find the gaps, risks and evaluate solutions. Find the gaps between current status and the ideal future state, identify risks and evaluate solutions to mitigate the risks.
- Create and implement a plan to bridge the gaps. For fixing the gaps, a plan is devised that includes Policies, their Implementation and the Audit of policies and implementation of controls.
Policy: A policy serves as a tool for comprehending the underlying principles of a guideline, which in turn mitigates specific risks. It aids in the definition of processes necessary to attain the desired outcome. Essentially, the policy addresses the “Why” (objective) of a guideline. Furthermore, it outlines the top-level ownership of the policy, specifying the individual or entity responsible for its implementation.
For example, the Board may prescribe that there should be a policy for ‘User Access’ to minimise the security risk of unauthorised access to physical and logical systems. This policy should be documented. It should be communicated to the concerned persons. It should be reviewed annually. For the ‘User Access’ domain (area), the CISO (Chief Information Security Officer) of the organisation is responsible.
Implementation: The ‘User Access’ policy should be subdivided into more manageable, measurable tasks known as controls. These controls specify the “When” (a specific timeframe), “Who” (the responsible owner and supporting team), and “How” (checklists and workflows) for implementing the standards.
When granting access to new users and managing access for existing ones, the system administrator is expected to adhere to these guidelines:

- Mandatory User Credentials: Every user is required to possess credentials, including a login ID and password, to access any system.
- Authorization Requirement: Access for users must be approved by an appropriate authority.
- Competency and Skill Verification: Access should only be granted to users who demonstrate competence and skill in using the system.
- Need-Based Access: Access should be provided based on a documented need.
- Access Termination upon Satisfaction: Access privileges should be revoked once the need for access is fulfilled.

Audit: The audit process may involve random sampling. During the audit, two key aspects are examined:
a. The existence of the policy, and
b. Whether the controls outlined in the policy are followed during the implementation phases, while seeking evidence to support compliance with these controls.
In the user access example, the audit committee’s review will encompass several aspects:
a. For the policy document on User Access:
- Assessment of the policy document itself.
- Determining its creation date.
- Identifying the date of its most recent review and approval.
- Establishing the individual or entity responsible for its implementation.
b. For the implementation audit:
- Selection of specific user access cases.
- Examination of when these users were granted access.
- Identification of the assets or resources to which access was granted.
- Verification of the authorizing entity or individual.
- Inquiry into the purpose behind granting access.
- Review of when access was subsequently revoked.
The A-P-I-A framework ensures that all the risks related to information security are identified through gap assessment; mitigated through the policies; the policies are implemented by breaking them down into controls; and the audit process ensures that the processes are being followed as intended.